Social media have almost become a starting point when connecting to the internet for most people. The fact that users internalize the services provided by social networks and make them an indispensable habit of daily routine has not only exposed them to various dangers, but also the sense of belonging they have created in time has turned into their reflections in real life. For some, this has even caused pathological problems.
While providing infrastructures and platforms that make it easier for users to connect with each other and to share content, social networks pose severe threats and risks having a deep impact on users’ internet security and privacy. Social networks induce risks directly or indirectly. In this post, we will try to address the security and privacy problems caused by social networks according to their implementations in both web and mobile environments. And, we should classify the sources of direct and indirect dangers that may arise from the social networks, and then address the related measures accordingly. So, it is possible to classify the sources of dangers or risks as follows:
- Metadata of contents shared in social networks
- Misconfiguration or lack of security/privacy settings in social networks’ profiles
- Third-party applications in social networks
- The mobile applications of social networks
- Big data and data mining in social networks
- Friends, circles or connections in social networks
- Cyber security threats and security vulnerabilities of social networks
- Social networks’ policies, terms of conditions
- Social networks’ extensions/plugins and cookies
Let’s go deeper on these matters/dangers/risks.
1. Metadata of Contents Shared in Social Networks
The contents shared via internet-connected smartphones or tables can reveal some private or secret information about individuals like geo-location, daily life or owned-device model/name. Any metadata or EXIF (exchangeable image file format) information can be easily analysed or extracted from the shared content over social media. And the extraction of such information is easy-peasy! Hence, someone can reach the location of your home, favourite places, daily routine and so on. So, how to defend yourself from metadata extraction? You can find some useful tips below:
- You should immediately disable GPS, geo-tagging or geo-location feature in your device’s camera or picture/video settings.
- You should not share the exterior or interior of your home. Because one can pinpoint your location from an exterior photo of your home by just searching in Google Street/Map/Earth or something similar.
- You should avoid sharing any crumb of information about you or your family in the social networks.
2. Misconfiguration or Lack of Security/Privacy Settings in Social Networks’ Profiles
The security and privacy settings of popular social networks (Facebook, Instagram, Twitter and so on) have lots of things to adjust. At some point, this confuses most users and causes them to leave their settings on the default. Maybe it is a sinister strategy through grossing out users to not harden their security and privacy settings.
So, users should firstly focus on their security, digital security and privacy on these platforms. Of course, it starts with the way of their usage or habit. Then, users should not be confused about them and just focus on the questions listed below. By answering these critical questions, users can easily adjust their settings in social networks:
- Did you set the two-factor authentication for login?
- Do you need geotagging (GPS or geo-location) enabled on your posts/tweets/sharing?
- Do you like face-tagging in any shared photos which show you?
- Do you want to be looked up by your e-mail or phone number on the social networks?
- Who can see your posts/tweets/photos/sharing?
- Are you comfortable with sharing of your information with advertisers?
You can find the related security and privacy settings on the social networks by visiting the links below:
- https://www.facebook.com/settings?tab=privacy
- https://www.facebook.com/settings?tab=security
- https://www.facebook.com/settings?tab=timeline
- https://www.facebook.com/settings?tab=location
- https://www.facebook.com/settings?tab=facerec
- https://www.facebook.com/settings?tab=followers
- https://www.facebook.com/ads/preferences/?entry_product=ad_settings_screen
- https://help.instagram.com/196883487377501
- https://help.instagram.com/116024195217477
- https://help.instagram.com/369001149843369
- https://twitter.com/settings/safety
3. Third-Party Applications in Social Networks
Third-party apps or games sometimes can be the most dangerous thing on the social networks. Because users generally overlook the third-party apps and their specific settings which connect and see the profile of users.
A third-party application used by a friend can expose any information from the user who does not use that application. So, your friend profile can convey your profile information by a third-party application unintentionally, even if you do not use it.
Furthermore, we sometimes can see how third-party apps endanger the whole social media ecosystem by not protecting the data they collect. They often cause unprecedented damage to users. At this point, the measures below can be very useful:
- users should not use a third-party app which they do not know how they collect and utilise their data.
- users should only choose the apps they need to do something.
- users must control the settings of applications and harden their configuration according to their needs:
4. The Mobile Applications of Social Networks
The mobile applications of social networks have long been known to collect contacts, location, browser history, SMSs, all online accounts attached to phone and call records from smartphones. Furthermore, they can take pictures and record videos unbeknown to the owner of the smartphone by surreptitiously accessing the camera.
Another concern is the cross-correlation of a user’s information dispersed across different social networks’ mobile apps and web apps. By this way, some companies can easily track and build a whole and clear profile of a user and target him/her around the internet.
Protecting from such invasive actions is not easy. So, users must frequently control the phone permissions that are given to apps and adjust the specific configuration form the related pages of social networks. As an example of contacts control in the social networks, you can see the link below:
- https://www.facebook.com/contact_importer/remove_uploads.php
- https://www.facebook.com/mobile/facebook/contacts/
- https://www.facebook.com/help/355489824655936
- https://www.facebook.com/mobile/messenger/contacts/
- https://www.facebook.com/help/838237596230667?ref=messenger_contacts
- https://twitter.com/settings/contacts_dashboard
- https://help.instagram.com/236691729788553
5. Big Data and Data Mining in Social Networks
The big data and data mining can easily distinguish users and disclose their private information on social networks. Whatever you do, it is nearly impossible to tackle. Users leave numerous data about themselves on social networks and then with some specific techniques and methods, the profiling of users suddenly emerges. Especially, the information left jauntily across the social networks yields very useful clues to reveal the complete profile of the users.
Through analysing a public/private social network’s profile, these things can be determined:
- where a user lives although the location is not given by the user,
- which community a person belongs to,
- how the users behave in future,
- and the weaknesses of an organization’s structure.
Much worse, the job of data mining goes one step further and social networks use big data to identify Internet users who are not members of them. So, social networks can obtain an enormous network of non-members through the e-mail addresses given by members to search for their friends.
Unfortunately, there is no permanent panacea against big data and data mining for now.
6. Friends, Circles or Connections in Social Networks
A user’s misconfigured social network’s privacy and security setting can affect negatively its friends as well. There is no limit to the dangers of spreading risks through content sharing to a friend from a user who did not properly set its settings. As such, the dangers of complex risks spreading over the same user’s third-party application have no limit too. However, the threats which emerge from social network users can be listed as follows:
- Fraudulent and deceptive users who impersonate a user’s real friend or a celebrity,
- Fraudsters whose job is to deceive or phish naive social network users,
- Compromised social network accounts,
- and common or mutual friends in social networks.
In an example, as a striking method, with the common or mutual friends feature in social networks, attackers can reach a user’s special information and connections. But there are some measures against the risks of social networks’ friends as below:
- Users should befriend with persons who they know closely in their real social life.
- Friends whose profile seem passive for a long time must be verified via traditional communication ways like a phone call or e-mail.
- Users should not share their very special information with social network friends even they are very close.
- Unused social games and third-party apps and their profile permissions must be deleted and revoked immediately.
- Users should never connect to their social networks account from the devices which they do not own.
7. Cyber Security Threats and Security Vulnerabilities of Social Networks
There several usual security threats around internet affect social networks users directly as classical threats like malware, phishing, CSRF (Cross-Site Request Forgery), XSS (Cross-Site Scripting) and as modern threats like clickjacking, typosquatting and cyberbullying. While some of these threats emerge from social networks’ sites/apps or infrastructure, the other threats may come from weak security controls in devices and lack of awareness. Social networks’ users should not be responsible for all of these threats or weakness. Although there are many measures that must be taken against all of these threats, nobody will able to achieve or incorporate them fully at the same time. As an end-user, you can check or control some of them below:
- Unnecessary personal information should be removed from social network profiles.
- Friendship/connection invitations from foreigners should not be accepted.
- Computers and mobile phones which are used for social networks should always have anti-virus, anti-malware, anti-spyware or security applications.
- Shortened URLs should never be clicked as long as they do not come from a trusted source.
- Social network profiles should not be opened in a public wifi internet and someone else’s devices.
- All devices’ software or firmware must be kept updated.
- Social networks never ask re-login after a successful login. In other words, you should be cautious about re-login requests from popup’s windows or apps.
8. Social Networks’ Policies, Terms of Conditions
When social networks offer free services, that does not mean they are like a mother embracing users without benefits. Users always pay with their information and social networks claim users always owe to them. But how? Social networks have special engagements/agreements/contracts that determine the relationship between them and their users; these can be named like “terms of service”, “terms of use”, “privacy policy”, “terms and conditions” and/or “data use policy”. When users want to use social networks, they become a contracting party of these agreements. All of these include very tying clauses.
Keeping this in mind, by just looking at two incidents occurred in the recent past, you will recognize how social networks treat you and your information:
This situation never changes. Social networks will continue to sell users’ data and develop services by utilizing their user-generated data (your photos, bio, demographic, social life and all). This is the business they have built upon it. Your data turns into their data after uploading or submitting whatever you want.
At this point, users can not solve the problem of misuse or privacy-invasive usage of their data by social networks. Governments and/or non-governmental organizations should take on a task, then they need to regulate social networks strictly and continuously.
9. Social Networks’ Extensions/Plugins and Cookies
Social networks have some tools for browsers, analytics, social sharing and content distribution. These can be a browser extension, a cookie, a web page plugin or specific scripting code that mainly are integrated with other websites around the internet. By these tools, social networks can track and follow you around the internet without exposing themselves. So, they are actually robust trackers. Hence, they know whatever you do on the web around the clock. As an example, even worse, Facebook secretly tracks a user for two years after deletion of its account and also knows self-censorship of users.
However, users can protect themselves to some extent from this invasive monitoring though the tools below. Some of them can be used in mobile devices too:
- Privacy Badger
- Disconnect
- Ghostery
- AdBlock
- My favorite is uBlock Origin for Firefox and Chrome
The Closing Words
In this long post, I tried to address the security and privacy problems of social networks in 9 main categories. We clearly saw that the fact that social networks do not charge for their services causes a great disadvantage in terms of the privacy of personal information. We have also observed that the spread of social networks on all communication platforms connected to the internet has created an increasing threat surface in time.
A secure state would be achieved provided that personal information in profiles is kept at the minimum, browsers and devices are up-to-date, and social profile settings are tightened. And this would only be temporary.
We also realized that continuous and periodic controlling of security and privacy at every point/level of social network usage is essential in the long term. Above all, we understood that the governments, non-governmental organizations or regulatory authorities should tightly regulate and control social networks.
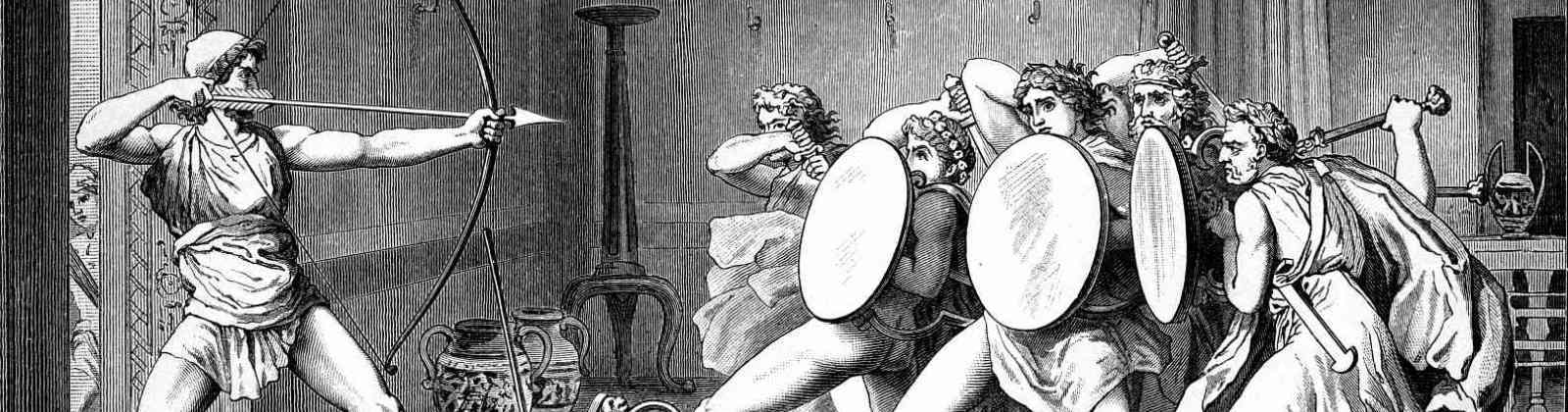
The featured painting above is “The Phaethon Legend: Fall of Phaethon and Olympian Gods” by Francesco Albani