Securing e-mail is a very heavy task due to its ancient infrastructure. Though this job should primarily rely on user awareness, there are a couple of measures that should be considered collectively such as security gateways, SPF, DKIM, DMARC, etc. But scanning of an e-mail message’s or body’s hash value in known malicious databases is useless.
Generating the hash value of an e-mail message or its body is a kind of brief signature of it. Hash values are assumed to be unique once they are generated. However, we need to understand whether e-mail messages are rendered or not.
SHA256 (raw e-mail message) ≈ HashValue1
SHA256 (rendered e-mail message) ≈ HashValue2
SHA256 (raw e-mail message + attachment) ≈ HashValue3
SHA256 (rendered e-mail message + attachment) ≈ HashValue4
[ HashValue1 ≠ HashValue2 ≠ HashValue3 ≠ HashValue4 ]
E-mail messages are generally rendered by e-mail clients or services you use. Otherwise they are not rendered. Once a message is rendered, it becomes a unique message regardless of the content of the message whether the attacker’s message is tailored or generic. Then if you take the hash of a rendered message and scan it against known malicious-dubbed databases, you will most probably get nothing important. Because it is sui generis and nobody will know it. So, this e-mail hash scanning is a useless security control against malicious or phishing e-mails.
If e-mail messages are not rendered by e-mail clients, we need to look at whether it is tailored or not. If the message is tailored, hash value checking will still be obsolete. If it is a generic message, attackers generally have to change the link’s parameters due to the need for the recipient’s click tracking. So the message’s links are not generic whereas its contents are generic. Then, the hash value for that type of message remains unique and useless.
To sum up, e-mail hash scanning is a waste of time and it is not a security control at all. However, the virus and malware scanning of e-mail attachments regardless of the e-mail message itself is a valid and useful security control.
Given these circumstances, for maintaining e-mail security of companies and institutions, there must always be periodic user awareness training, secure protocols used, an e-mail security gateway and web filtering proxy correctly deployed, and SPF, DKIM and DMARC settings properly implemented.
Also, there are a few links below that are worth mentioning:
- https://blog.jonlu.ca/posts/spf-dkim
- https://www.praetorian.com/blog/email-security/
- https://github.com/Rices/Phishious
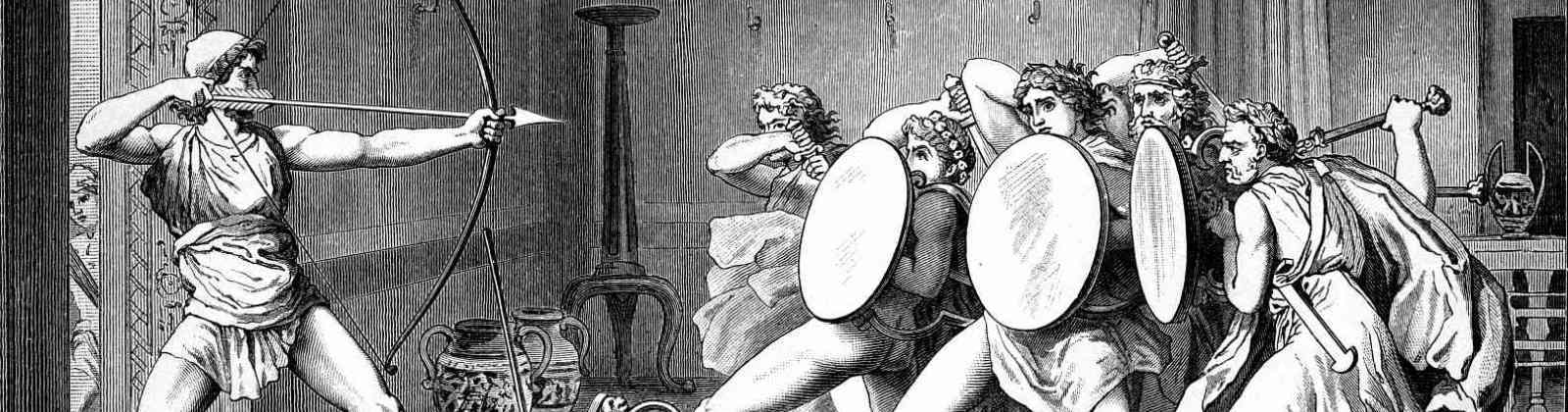
The featured painting above is Battle of Alexander versus Darius by Pietro da Cortona