The tool which can find its real meaning from its user’s scenarios and sine qua non inputs is a Security Orchestration Automation and Response (SOAR) platform. By bringing productivity growth in security workflows, harmonizing security tools for multiple purposes, providing flexibility into your security architecture and accelerating decision-making process, SOAR is mainly used for security operations centres (SOC) but it also can help other security operations. And it facilitates unloading your anger against most of the threats in a controlled manner.
While SOAR is a centralized control hub, the playbooks are vital scenarios, and sine qua non inputs are a perfectly performing SIEM and an indispensable threat intelligence. In case of insufficient or flawed scenarios and ruined inputs, SOAR will be as useful as a chocolate teapot. In this post, I will try to design some useful playbooks to run in your environment, bearing in mind that SIEM and threat intelligence are already in play. The playbooks below are designed according to the most restricted actions. The scenarios depend on several factors such as your business, your IT environment, the legal and regulatory compliance and so on. You can expand or detail the scenarios according to your needs:
- Phishing or Spear-Phishing
- End-User and Endpoint
- Security Maintanance Operations and Diagnotics
- Threat Hunting and Malware Analysis
Phishing or Spear-Phishing
- Alarms/alerts of suspicious e-mails feed the SOAR from various resources like your anti-phishing tool, SIEM or e-mail security gateways.
- The SOAR dissects important indicators of compromise (IOC) such as sender IP, e-mail address, attachments, subject and so on as a requirement of the triage process. Later, simultaneously:
- It checks and evaluates reputation or severity of incoming data by cross foot checking the data against reputation services and threat intelligence sources.
- It sends content or attachments to a sandbox for further analysis.
- If the result of one of the actions above is positive, the security operators and the affected users are informed with the detailed instructions. At this point, suspicious becomes malicious. At the same time, the SOAR also scans all e-mail accounts to locate other malicious e-mails and then deletes them. Later the SOAR informs other security tools for blacklisting the malicious IOCs.
- If the result of one of the actions in the second step is negative, the SOAR forwards the case to the security team for a manual investigation. If the manual investigation is assessed as “clean”, then the SOAR closes the case and sends the original e-mail to the owners.
End-User and Endpoint
Several attacks may be started from endpoints or by end-users such as failed login attempts, login attempts from unusual locations or devices, same user logins from different places and so on. You can see some of the end-user or endpoint scenarios below:
Failed Logins
- When the number of failed logins on a service/device exceeds the allowed threshold, the SOAR warns the affected end-user to confirm whether it is legitimate:
- If the end-user verifies the attempts with “legitimate” response, the SOAR platform resets the password and informs the affected end-user with the required information.
- If the end-user confirms that it is illegitimate, the SOAR confirms the account takeover attempt, simultaneously investigates the details like the IP and location of the failed attempts and quarantines the affected endpoint.
Unusual Logins
There may be multiple unusual login types that depend on your business or environment. In one example, when end-users are connected to the company VPN service, same end-user’s login activity may be seen at the workplace location in time that cannot happen as quickly as the two logins occur. In the other example, it occurs when end-user logins from an unusual place or on a new device other than its likely geographical location/IP. In such scenarios:
- for reconciling and cross-checking time, IP and login information, the SOAR seems able to query Active directory service, geo-IP lookup, NTP service, the VPN service, the workplace’s point of entry/exit data and so on.
- once catching a different IP address other than likely original IP blocks, the SOAR warns the affected user to verify its exact location. If the user responds as “an illegitimate action”, the SOAR blocks the suspicious IP and notifies the security team for further investigation.
Security Maintanance Operations and Diagnotics
The SOAR can be used for security maintenance or diagnostics operations. For this type of purposes, you can see the example usages below:
- the SOAR can query your certificate management tool to check the expiration status of SSL certificates of any servers/endpoints. For problematic certificates, the SOAR informs the affected user or the certificate’s manager by finding the related user details from the Active Directory.
- the SOAR can identify unmanaged endpoints in terms of antivirus, DLP or any endpoint agents. If any endpoints are out of control or down, the SOAR can ping/wake the agents, open tickets or escalate the case.
- The SOAR can query the vulnerability management tool for any diagnoses, consequences, results, reports and remediations related to a specific vulnerability or endpoint/server. At the same time, it can correlate the data with data from other relevant security tools. Hence, based on the gathered correlated data, the SOAR can assign the severity of the incident/vulnerability and escalate the situation for manual investigation and remediation.
Threat Hunting and Malware Analysis
- If a malicious indicator is found by other resources/tools, the SOAR can feed other security tools with the finding and update watch lists. Also, the SOAR can check all endpoints/servers to identify if other endpoints have been compromised by the same malicious indicator, and take further actions such as quarantining, opening tickets and so on.
- For identified indicators or unidentified things, the SOAR can trigger the endpoint tool to kill malicious processes or neutralize/delete infected files.
- The SOAR can collect data from a wide variety of sources such as SIEM, endpoint tools, Exchange servers, threat intelligence feeds, malware analysis tools, etc and then extract any files that need to be neutralized.
Useful Resources
You can find very useful resources below that provide tricks and methods for playbooks to implement in your environment.
- https://www.recordedfuture.com/incident-response-soar/
- https://www.recordedfuture.com/soar-use-cases/
- https://www.rapid7.com/info/security-orchestration-and-automation-playbook/
- https://www.dflabs.com/resources/blog/5-common-security-orchestration-automation-and-response-soar-use-cases/
- https://www.infosecurityeurope.com/__novadocuments/544304?v=636821081002000000
- http://pages.siemplify.co/rs/182-SXA-457/images/Top_Security_Playbooks_for_2019.pdf
- https://em360tech.com/sites/default/files/2020-09/8-Real-World-Use-Cases-for-SOAR-e-book-_-Swimlane%20%281%29.pdf
- https://dnif.it/soar-security-orchestration-automation-response-guide.html#security-automation-use-cases
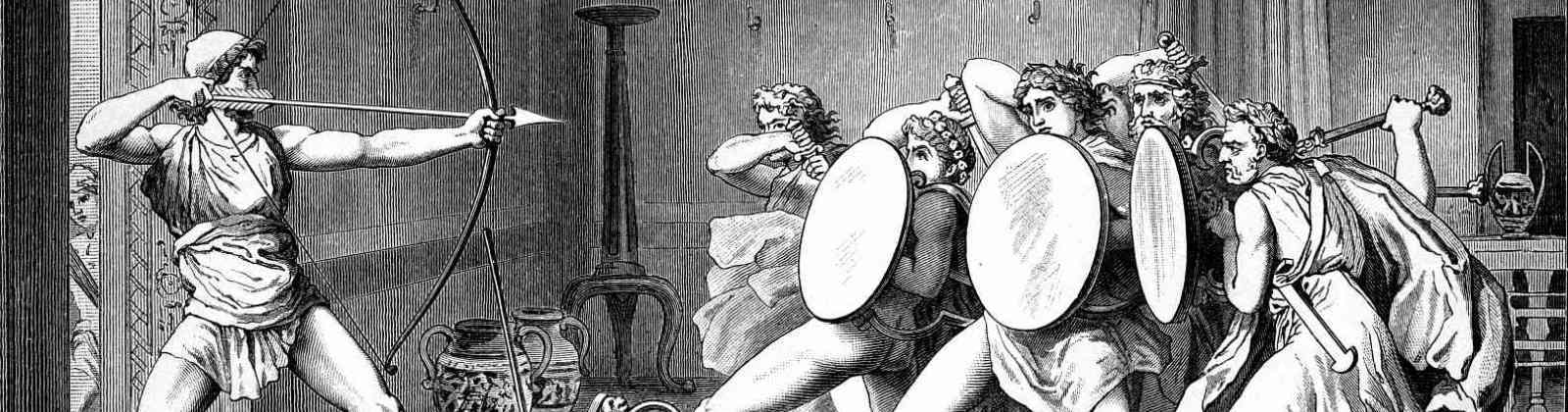
The featured painting above is from Charles-Antoine Coypel: Fury of Achilles