In terms of cyber security capability, undisputedly, Google and Microsoft have both security analytics, web scanning and classifying, machine learning (ML), artificial intelligence (AI), user and entity behaviour analytics (UEBA) alongside diverse intelligence resources. Hence, we can accept them as of equal strength in the capability and resources. But this situation may differ in details. And some details can change the game.
If both rivals have similar tools and capability, then the quality and fine details of cyber threat intelligence resources can be decisive in which the opponent may beat the other in this long-running of struggle. And, when comparing the cyber intelligence power of both rivals, we should focus on the details of cyber threat intelligence data granularity and its quality. The more qualified and detailed threat intelligence data you have, the more insightful and effective results you get. As an analogical example, to simply put, your SIEM system is only as effective as your log resources – except its correlation capacity and capability. In other words, if you have very detailed and useful logs about a system or an application then you can see the events or incidents more broadly and comprehensively. Then, we need to find out the answer of who has the most detailed and useful log for the time being in the cyber threat intelligence.
As threat landscape evolves constantly, identifying important indicators of compromise (IOC) such as threats conveyed by e-mail, download, clicks, files or attachments; threats communicated through IP, domain or URLs; threats infected file, DLL, process or registry keys; or threats caused anomalies, irregularities or violations during the cyber kill chain become critical.
So, who can collect the most valuable and detailed logs beyond general IOCs on a global scale? Going back to our comparison, we see only two distinctive featured tools for both Google and Microsoft. We see, Microsoft has the Windows Error Reporting (WER) system and Google has the VirusTotal. These featured tools are not identical or similar. And both of these featured tools seem sui generis regarding cyber threat intelligence.
VirusTotal Microsoft Lacks
VirusTotal, as one of the largest malware intelligence services in the world, provides multi-scanner malware insights. Once you upload a file, you get free assessments that include verdicts from more than 50 antivirus products. You can use it to perform basic research about malware and to uncover the relationships between malware files, domains, and IP addresses. You can reach some detailed information about a file by depending on a global scale malware engine. As we know, Microsoft does not have such a broad analysis tool supported by the security industry. It seems almost impossible for Microsoft to vie with VirusTotal. But we have to add that the job of VirusTotal is a dynamic analysis which is performed systematically in a predefined and controlled environment.
Windows Error Reporting (WER) Google Lacks
The omnipresence of the Windows operating system and other Microsoft’s products enable Microsoft to continuingly sense what happens on the internet. Such widespread usage around the world gives Microsoft unprecedented power for threat intelligence though undoubtedly it causes big privacy problems.
Microsoft products already have a built-in Windows Error Reporting (WER) mechanism that continuously collects data from any of Microsoft’s product in use, so it finds out bugs or malfunctions through telemetry. Moreover, an article gives interesting information from the inside, saying Microsoft’s security teams have already turned this telemetry system into unique and powerful security tools which nobody else has yet. By this way, Windows machines around the world reach out to Microsoft, then all the data collected from machines are reported to Microsoft utilizing telemetry. Hence, Microsoft can analyse the mass of data to find out security incidents before anyone else. So, Microsoft WER resembles a static analysis. The best part of this telemetry is that the data comes from a live environment not one like a predefined and controlled environment. Eventually, every Windows machine is a threat intelligence source that feeds Microsoft and its cloud constantly. Of course, Microsoft extracts any signals from your security telemetry or WER files to find threats instantly. And Google does not have such a powerful tool.
That’s the thing that nobody else has: visibility and data. The data that nobody else has is around those application crashes at the operating system and the software layer. Even for third-party crashes, they have telemetry around those. As you start looking at exploit targets, Microsoft has the ability through their telemetry. Microsoft sees stuff that just nobody else does.
Jake Williams, a former member of the National Security Agency (NSA)
The Closing Words
To assess the level of cyber threat intelligence power or security capability associated with these trust companies, their security platforms should be compared across many criteria through a side-by-side comparison of the key components/tools associated with them. But they seem to fight behind the curtain. We can only follow bread crumbs, read between the lines, track their declarations and see the products they publicly show. Also, we assume they have unlimited or sufficient budget to run the race. Referring to our previous simple SIEM analogy, since it gets and sees the most detailed log, Microsoft seems to be the front runner of this race for now.
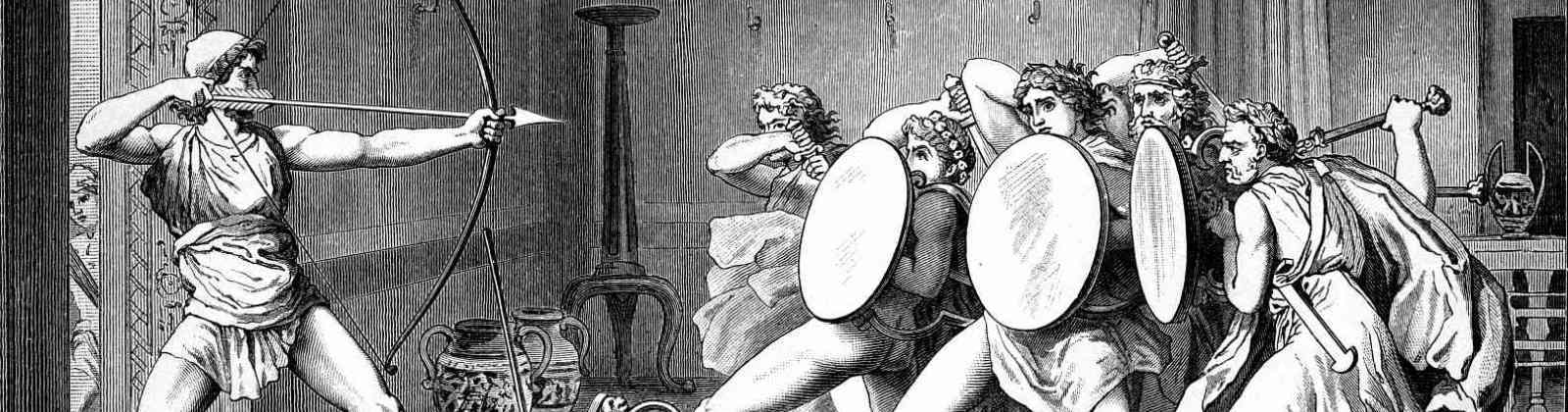
The featured painting above is “The Lost Leonardo: Peter Paul Rubens’s copy of The Battle of Anghiari (Leonardo da Vinci)“.